Azure Arc is a service that provides a set of technologies for organizations management that want to simplify their complex and distributed environments. With Azure Arc, Microsoft offers simplified management to resources running inside and outside of Azure.
Prosegur – a big company with a big footprint in five Data Centers around the world and workload in Azure, AWS and Google. They choose Azure Arc as solution to manage their on-premises servers and multicloud environments “because it has the capability to cover all the scenarios that deal with on-premises but also with other clouds. Azure Arc is one of the best tools to manage a fleet of servers”.
When a server is connected to Azure, it becomes an Arc enabled server and is treated as a resource in Azure. Each Arc enabled server has a Resource ID, a managed system identity, and is managed as part of a resource group inside a subscription. Using Azure Arc, you can manage these resource like they were in Azure. This includes:
- Manage resources through the Azure portal
- Apply Azure RBAC to these resources
- Apply Azure Policy to these resources
- Monitor these resources with Log Analytics and Security Centre
- Audit with Azure Activity Logs
- Query with Azure Resource Graph
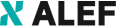
In summary, Microsoft is enabling Azure to manage the below services deployed externally:
- Windows and Linux servers running in bare metal, VMs, and public cloud IaaS
- Azure Stack HCI
- Kubernetes clusters
- Data services based on SQL Azure and PostgreSQL Hyperscale
- Applications packaged and deployed as microservices running on Kubernetes
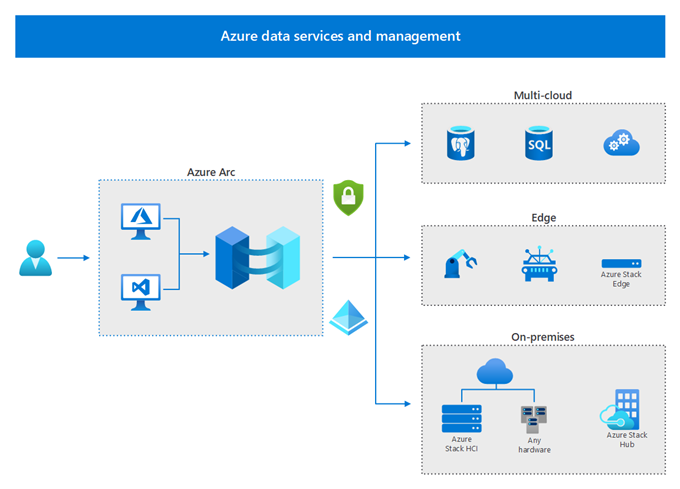
VM Setup
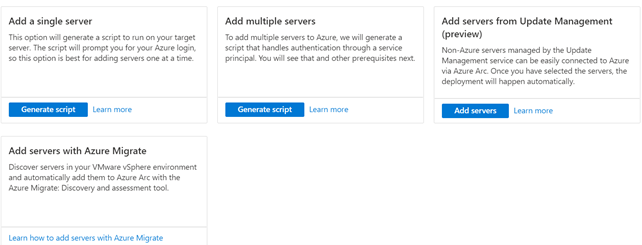
We click the button “Servers” and “add”, and the next page asks how we want to onboard machines. We have the option of either doing this manually by using a script or using automation to bulk add lots of devices.
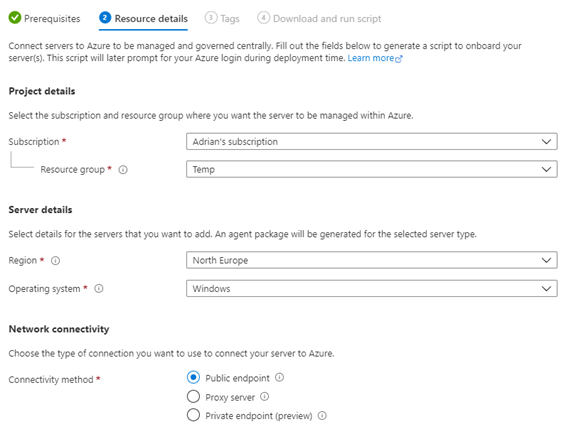
When we press the “Generate script” button, we need to supply some details about where this VM should sit once imported, which subscription, resource group and region. We also need to select an OS.
There are some prerequisites, which we have to choose if we want to connect a server.
- The server requires access to port 443 and a set of outbound URLs for the Azure Arc agent to properly function.
- Onboarding will require local administrator permission on the server.
- You can connect to the internet over a public endpoint, through a proxy server, or over a private endpoint. An Azure Arc Private link scope is required to connect over a private endpoint.
Next, we have to complete necessary fields in Project details.
The last step: download and run the script. Now we have this script; we can go ahead and run it on our VM. This script will go out and download the Azure Arc agent onto the machine, install it and then connect to Azure to register the VM. When you run the azcmagent connect command, you will be prompted to log in to Azure using the device login; this authenticates you to Azure to register. If you don’t want to do this manually, you can look at the bulk addition option which uses a service principal.
After you connect to your non-Azure VM, you’ll have access to multiple monitor options. The most interesting from my point of view is:
1. Policies. Assign Azure Policy guest configurations using the same process you use when assigning policies to your Azure VMs.
2. Monitor your connected machines' guest operating system performance.
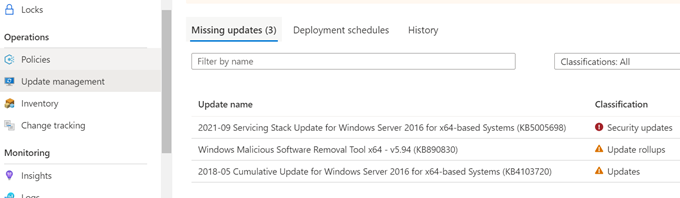
3. Update Management. With its help you can manage all updates, as well how we get used with WSUS.
All the resources registered with Azure Arc send the logs to the central, cloud-based Azure Monitor. This is a very powerful approach in deriving insights from highly distributed and disparate infrastructure environments.
Finally, Azure Automation service can be used to perform mundane to advanced maintenance operations across the public cloud, hyrbid cloud and multi-cloud environments.
Why would I want to use Azure Arc
As the customer Prosegur uses it to manage a complex environment of hundreds of servers. Azure Arc is aimed at clients who have machines outside of Azure that they need to manage, and who have already invested in Azure as their primary cloud. If you have already set up RBAC and Policies in Azure, then being able to apply these to external machines could make your governance and security much more consistent and easier to manage.
Extending beyond VMs into Kubernetes also means that Azure Arc can help you manage policies across your Kubernetes estate, enforcing best practice.
The ability to include machines in Log Analytics, security centre and have activity logs also means you can get your logs and audit all in one place, in a consistent format.
References: